The Importance of Blockchain Security and How to Prevent Threats Before They Strike
Learn why blockchain security matters and how to prevent threats with smart practices in blockchain development and trusted development partners.
Blockchain technology has earned a reputation for being secure, transparent, and decentralized. However, as adoption increases, so do the risks. While the underlying technology is robust, the real-world applications built on top of blockchains often introduce vulnerabilities that bad actors can exploit. Whether you're a startup planning a token launch or an enterprise integrating blockchain into your operations, ignoring security could be a costly mistake.
In this post, we’ll unpack the importance of blockchain security, explore real risks that developers and users face, and provide practical strategies to mitigate these threats before they escalate. If you're involved in blockchain development services or looking to partner with the best blockchain development company, this guide is your first line of defense.
Why Blockchain Security Is Critical
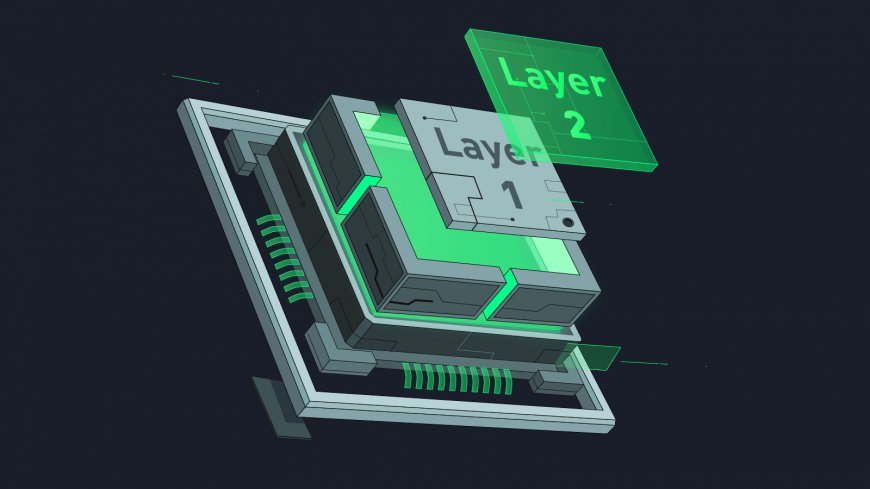
At its core, blockchain is a distributed ledger system that maintains a continuously growing list of records, called blocks, linked and secured using cryptography. The decentralized nature of the technology offers resistance to data tampering and unauthorized access. However, the system’s security depends on more than just cryptographic principles.
Real-World Use Amplifies Risk
In theory, blockchains are immutable and highly secure. In practice, applications built on them—like smart contracts, decentralized apps (dApps), and exchanges—can have loopholes. And these are what hackers often target.
More than $3 billion was stolen from blockchain platforms over the last year due to vulnerabilities in smart contracts, poorly secured private keys, and protocol logic errors. Many of these incidents could have been prevented with better security practices during the development phase.
Once It's Live, It's Final
Unlike traditional applications, where bugs can be patched easily, blockchain operates on immutability. Once a smart contract is deployed, changing its code is not straightforward. This makes proactive security measures essential. Prevention is not just better than cure—it's often the only option.
Key Threats in the Blockchain Ecosystem
To understand how to protect blockchain applications, it’s important to identify what kinds of threats developers and companies face.
1. Smart Contract Vulnerabilities
Smart contracts are self-executing programs that run on the blockchain. They automate transactions and workflows without human intervention. However, they are also a common target for attackers.
Common issues:
-
Reentrancy attacks
-
Integer overflows/underflows
-
Unchecked external calls
-
Logic flaws
-
Poor input validation
These bugs can allow attackers to drain funds, manipulate contract behavior, or lock resources.
2. Private Key Mismanagement
Private keys are like the master keys to blockchain accounts. If stolen, the attacker gains full control over the associated assets. Unfortunately, many breaches are due to poor key storage practices.
Risks include:
-
Storing private keys in plain text
-
Lack of multi-signature wallets
-
Weak or compromised seed phrases
3. Endpoint Attacks
Even if the blockchain protocol is secure, the endpoints that interact with it—like wallets, APIs, or user interfaces—may not be.
Phishing, malware, and browser vulnerabilities can compromise user credentials or transaction signing tools.
4. 51% Attacks
This occurs when a group gains majority control over the blockchain’s computing power (hashrate), allowing them to reverse transactions or double-spend coins. While rare on larger blockchains, smaller or newer networks are vulnerable.
5. Bridge Exploits
Blockchain bridges connect different chains, enabling interoperability. But they are complex and often under-secured. Many high-profile exploits have occurred via poorly designed bridge logic, causing massive losses.
How to Prevent Threats Before They Strike
Given these potential threats, it’s critical to embed security into every stage of blockchain development. Below are proven strategies to mitigate risk.
1. Perform Thorough Code Audits
Auditing is not just a box to tick—it's essential. Before deploying any smart contract, the code must undergo a detailed security audit by experienced professionals.
Best practices:
-
Static and dynamic analysis
-
Automated vulnerability scans
-
Manual review by multiple auditors
-
Include unit and integration tests for edge cases
Audits help uncover logic errors, security flaws, and potential exploits that might otherwise go unnoticed.
2. Use Established Security Frameworks
Don't reinvent the wheel. Use well-tested frameworks and libraries. OpenZeppelin, for instance, offers battle-tested smart contract libraries that adhere to best practices in Solidity development.
Advantages:
-
Reduces bugs from custom code
-
Ensures compatibility with major tools
-
Includes audit-friendly architecture
By using such tools, blockchain development becomes more reliable and secure.
3. Embrace Formal Verification
Formal verification involves using mathematical methods to prove that a program behaves as intended. It's especially useful for high-value or mission-critical smart contracts.
This approach minimizes the risk of hidden logic bugs that may not surface in conventional testing.
4. Secure Private Key Infrastructure
Private key management must be a priority.
Recommendations:
-
Use hardware wallets or HSMs (Hardware Security Modules)
-
Implement multi-signature wallets for fund custody
-
Avoid storing keys in cloud services or exposed environments
In enterprise contexts, partnering with a best blockchain development company often includes secure key management as part of the package.
5. Deploy Bug Bounty Programs
Even with internal audits, some bugs might slip through. A bug bounty program incentivizes external researchers to report vulnerabilities before they’re exploited.
These programs are cost-effective and have been used successfully by major platforms to enhance security.
6. Continuous Monitoring and Logging
Monitoring blockchain applications in real-time can help detect anomalies, suspicious transactions, or potential exploits.
Monitoring elements:
-
Smart contract activity
-
Transaction volume spikes
-
Gas usage anomalies
-
Wallet activity patterns
Using tools for threat detection and real-time alerts is essential to responding quickly if an issue arises.
7. Plan for Governance and Upgradability
In traditional software, rolling out a patch is straightforward. In blockchain, it’s complex due to immutability. Designing contracts with upgradability features or proxy patterns can make future updates easier.
Governance mechanisms, such as DAO voting, allow for decentralized decision-making around upgrades and fixes.
The Role of Professional Development Teams
Security is a specialized field. Partnering with a best blockchain development company ensures that your project is not only functional but fortified against known and unknown threats.
Professional firms provide:
-
Security-focused architecture planning
-
In-house and third-party audits
-
Secure DevOps pipelines
-
Regulatory and compliance readiness
-
Ongoing maintenance and updates
A good development partner won’t just write code—they’ll embed security throughout the application lifecycle.
Realistic Roadmap to Secure Blockchain Development
If you're starting a blockchain project, here’s a realistic path to secure development:
-
Define scope and risk level – Know what’s at stake.
-
Design secure architecture – Minimize complexity and expose fewer attack surfaces.
-
Develop with secure coding practices – Follow best practices for the chosen language/platform.
-
Conduct internal testing – Cover edge cases, stress tests, and failover handling.
-
Undergo third-party audits – Bring in external experts to validate code.
-
Launch with security controls – Use rate limits, access controls, and logging.
-
Monitor post-launch – Be ready to react and patch vulnerabilities swiftly.
Each step must include security considerations. Rushing to market without proper safeguards is a gamble that could result in millions lost, reputations ruined, or legal consequences.
Final Thoughts
Blockchain offers game-changing potential across industries—from finance and supply chains to healthcare and gaming. But its benefits come with high stakes. A single vulnerability in a smart contract or a poorly managed key can result in catastrophic losses. Prevention is not just advisable—it’s essential.
Whether you're building from scratch or scaling an existing project, prioritizing security in every phase of blockchain development is non-negotiable. And if your team lacks the expertise, partnering with the best blockchain development company is a wise investment. They bring not just code, but a security-first mindset backed by experience, tools, and a deep understanding of potential threats.
In the evolving world of decentralized systems, you can’t predict every attack—but you can be ready. Start with secure practices, plan for the worst, and build with confidence.



 snehawt15
snehawt15 






