IP Address Mistake That Is Quietly Killing Your SaaS Analytics, Security, and Compliance in 2026
There is a problem sitting inside your production logs right now. It is not a bug. It is not a misconfigured server. It is something far more subtle, and far more damaging: your platform is almost certainly handling IP addresses in a way that produces inaccurate analytics, weakens your fraud detection, and quietly breaks your compliance reporting. And the root cause comes down to one fundamental concept that most engineering teams think they already understand.
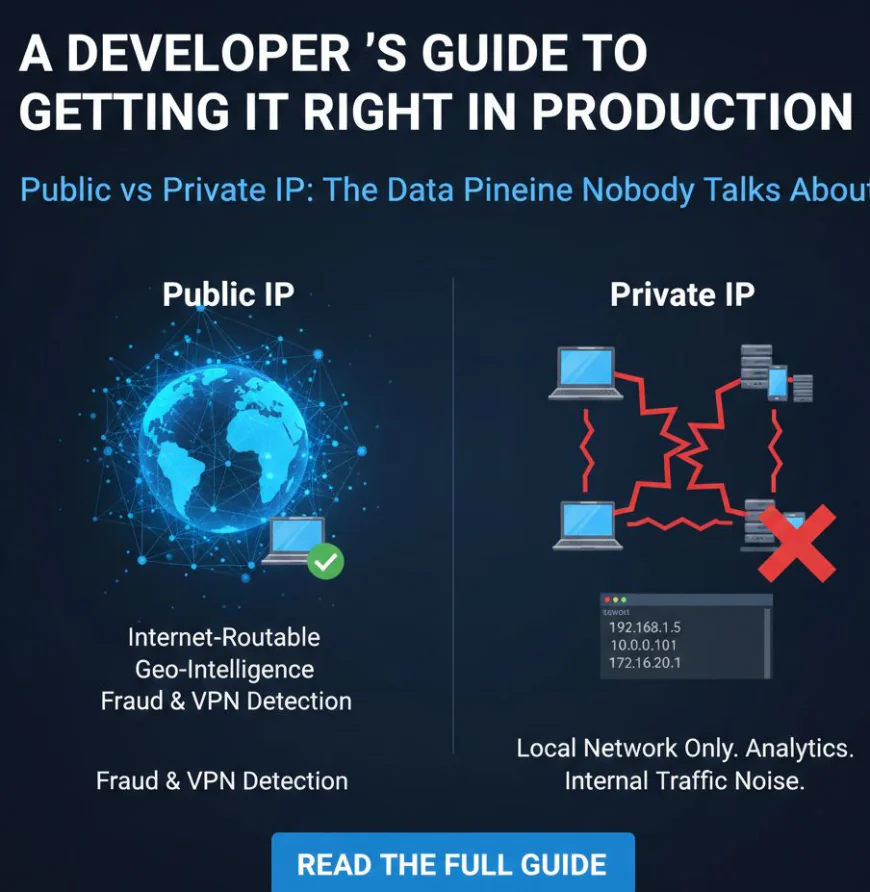
The difference between a public IP address and a private IP address.
What Most Teams Get Wrong From Day One
Here is what typically happens. A request arrives at your server. An IP address is logged. That IP address is then passed downstream to your analytics stack, your geolocation service, your fraud scoring engine, or your compliance pipeline. Everything appears to be working. Dashboards are populated. Alerts are firing. Reports are being generated.
But if the IP address being logged is a private IP, none of that downstream processing means anything. Private IP addresses, which fall within the reserved ranges of 10.x.x.x, 172.16.x.x to 172.31.x.x, and 192.168.x.x, are internal network identifiers. They exist only within local environments. They carry zero geographic information. They cannot be mapped to a country, a city, a timezone, or a risk score.
And yet they appear regularly in production logs, passed to APIs and pipelines that were built to handle public IPs, silently returning empty results or defaulting to fallback values that distort every metric they touch.
The NAT Problem Nobody Talks About at Scale
Even when the correct public IP is being captured, there is a second layer of complexity that catches teams off guard. Most enterprise and institutional traffic is routed through a mechanism called NAT, or Network Address Translation. NAT maps hundreds or thousands of internal private IP addresses to a single shared public IP address before traffic leaves the network.
What this means in practice is striking. An office of 600 employees all hitting your SaaS platform during business hours may appear in your logs as a single user. A university campus. A call center. A shared coworking space. All of these environments produce traffic that is indistinguishable at the IP level without enrichment data that provides context about the connection type, the ASN, and the ISP behind that IP.
This is why raw IP counts in analytics dashboards are almost always misleading when enterprise traffic is involved, and why user attribution at the IP level requires a much more intelligent approach than most teams currently implement.
VPNs Have Changed the Game Permanently
In 2026, VPN usage is no longer a niche behavior. Remote work policies, privacy awareness, and the normalization of consumer VPN products mean that a significant and growing portion of your user base is connecting through VPN exit nodes. What your server sees is not their real public IP address. It is the IP address of the VPN provider's server, which may be located in an entirely different country.
The downstream consequences of this are serious. Time zone assignments become incorrect. Regional analytics become distorted. Impossible travel detection fails to fire when it should. Geo-restricted content policies become unenforceable. And fraud scoring systems that rely on IP reputation data are working with information that does not reflect the user's actual network context.
Without automated detection of VPN usage, proxy services, TOR exit nodes, and hosting provider IPs, your security and analytics stack is operating with a significant blind spot that grows larger every year.
What a Properly Built IP Intelligence Layer Looks Like
The solution is not complicated, but it does require intentional implementation. The correct public IP must be extracted from each incoming request, with proper handling for proxy headers such as X-Forwarded-For and load balancer forwarding rules that can otherwise cause internal addresses to be logged instead of the original client IP.
Once the correct public IP is in hand, it needs to be enriched. This means passing it to an IP intelligence API that returns structured metadata including the user's country, city, timezone, currency, ASN, ISP, connection type, proxy status, VPN flag, TOR node status, and threat level. APIs like IPstack provide exactly this, with continuously updated datasets that reflect current IP allocations, emerging VPN infrastructure, and real-time threat intelligence.
This enriched context is then what powers accurate analytics, correct timezone handling, meaningful fraud detection, and defensible compliance reporting across your entire platform.
The full technical breakdown of every concept covered here, including how to classify IPs correctly, how NAT affects visibility, how VPN detection works in practice, and how to integrate IP enrichment into a production pipeline, has been published in this comprehensive guide:
? Public vs Private IP Addresses: A Complete Guide for SaaS and Enterprise Teams
If your platform collects, logs, or acts on IP address data in any capacity, this guide covers everything your team needs to get it right. The problem is more common than most teams realize. The fix is more accessible than most teams expect.
Frequently Asked Questions
Is it possible that my platform is logging private IP addresses without my team realizing it?
Yes, and it is more common than most teams expect. When requests pass through internal load balancers, reverse proxies, or misconfigured middleware, the IP that gets logged can easily be an internal network address rather than the original client IP. Auditing your request headers and logging pipeline is the first step toward catching this.
If multiple employees share one public IP through NAT, how can individual users be identified?
IP address alone cannot reliably identify individual users in a NAT environment. Additional signals such as session tokens, device fingerprinting, user agent data, and authenticated user IDs need to be combined with IP intelligence to build a complete picture of user attribution.
Why does VPN detection matter if the user is simply protecting their privacy?
VPN detection is not about blocking privacy-conscious users. It is about understanding the context of a connection accurately. A user connecting through a residential VPN looks very different from a bot farm routing requests through a commercial hosting provider. IP intelligence APIs provide this context so that risk scoring can be calibrated correctly rather than treating all VPN traffic the same way.
Can IP intelligence replace cookie-based tracking for analytics?
IP intelligence is not a direct replacement for cookie-based analytics, but it is a powerful complement. It provides session-independent context about the origin, connection type, and geographic attributes of a request, which is particularly valuable in environments where cookie consent has been declined or where server-side analytics are preferred over client-side tracking.
What is the first thing an engineering team should do to improve their IP handling?
Start by auditing what IP address is actually being logged for incoming requests. Compare it against the known private IP ranges to check whether internal addresses are ending up in your logs. Then verify that your geolocation and enrichment API calls are returning meaningful results rather than empty responses, which is a reliable indicator that the wrong IP is being used as input.
? Public vs Private IP Addresses: A Complete Guide for SaaS and Enterprise Teams










